BestCrypt Volume Encryption
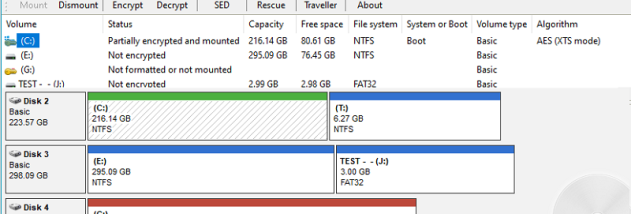
... Windows 10 download page for the renowned "BestCrypt Volume Encryption" software, a cutting-edge product developed by the industry-leading ... ultimate solution for comprehensive data protection, offering robust encryption for all volumes on your hard drives. BestCrypt ...